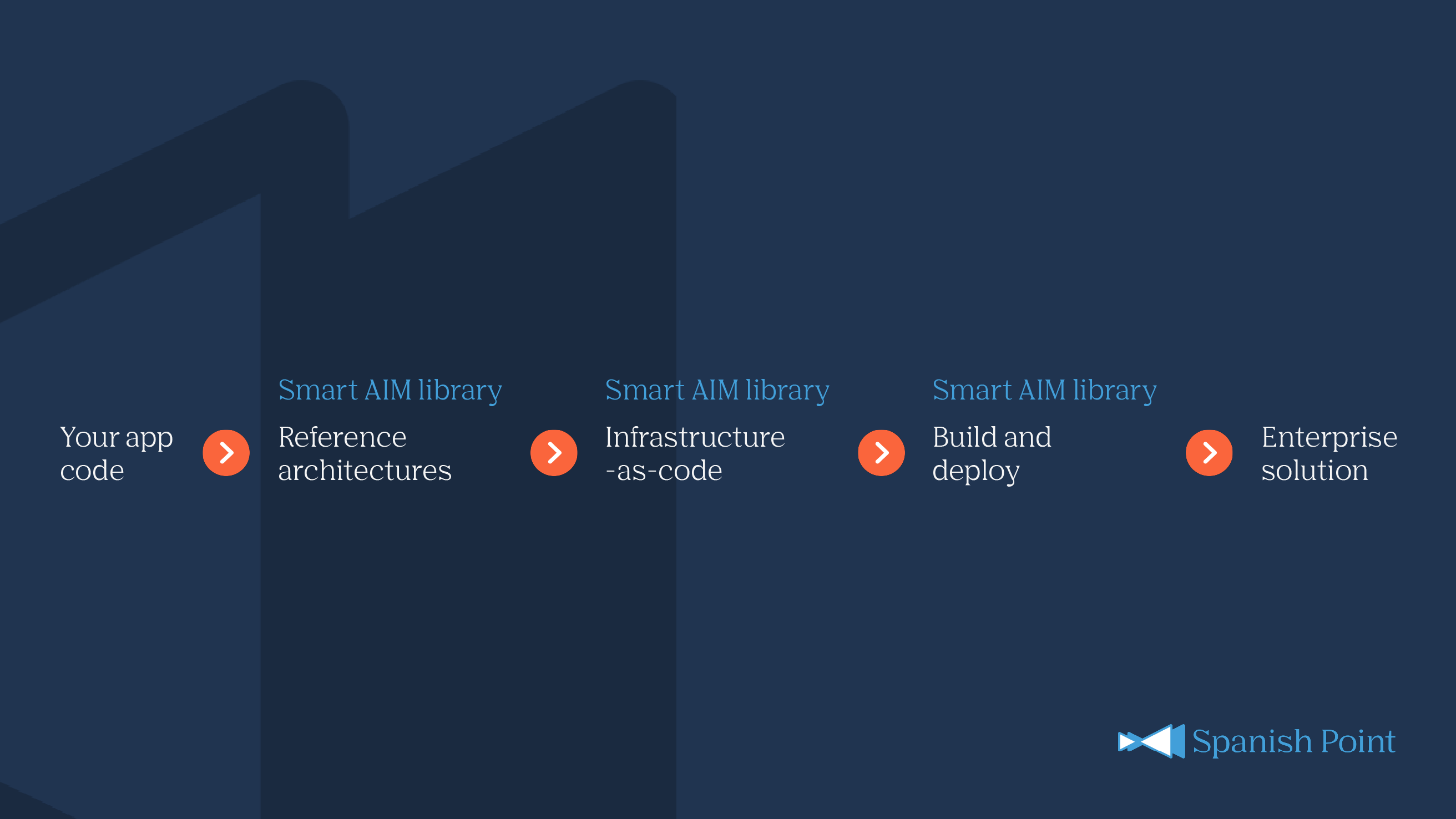
Smart AIM library
The Smart AIM library is a comprehensive collection of IaC and CI/CD templates for common Azure PaaS and IaaS components, with accompanying reference architectures for best practice assembly of the components with code to accelerate enterprise solution delivery.
Provisioning with Smart AIM library
The Smart AIM library consists of infrastructure-as-code for automated provisioning and configuration of Azure resources, DevOps pipeline templates for building application code and deploying the code and infrastructure to Azure, and reference architectures for industry best-practice assembly of infrastructure to support the application in a secure and scalable manner.